Test Data Encryption: Key Practices for QA Teams
Treat test data like production: use AES-256, strict key management (KMS/HSM), masking or tokenization, and automated CI/CD checks to reduce breach risk.

Test Data Encryption: Key Practices for QA Teams
87% of data breaches involve test environments, costing businesses millions annually. QA teams often handle sensitive information like PII and payment data, yet many fail to secure test data properly. Encryption is a must - not just for compliance with regulations like GDPR and HIPAA but to reduce breach risks by up to 90%. Here's what you need to know:
- AES-256 is the most reliable encryption for securing large datasets.
- Use RSA or ECC for secure key exchanges.
- Separate test, staging, and production keys to limit data exposure.
- Automate key rotation and use tools like AWS KMS or HashiCorp Vault for secure key storage.
- Protect data at rest and in transit with encryption and protocols like TLS 1.3.
- Avoid outdated methods like DES or RC4.
Encryption alone isn’t enough. Combine it with data masking, tokenization, and role-based access controls to protect test environments. Regular audits, automated CI/CD encryption tests, and proactive monitoring ensure long-term security and compliance. Treat test data as production-level sensitive - because breaches don’t discriminate.
Mastering Playwright | Encryption of Credentials with CryptoJS| QA Automation Alchemist
sbb-itb-eb865bc
Encryption Basics for QA Teams
Symmetric vs Asymmetric Encryption Comparison for QA Teams
Understanding encryption is crucial for QA teams aiming to safeguard test data. At its core, encryption converts readable data into a scrambled format, which only authorized users can decode. The method you choose depends on the type of data you're protecting and how it will be used.
Common Encryption Algorithms
AES-256 is a cornerstone of modern encryption. As Priya Mervana from SSLInsights puts it:
"AES is widely regarded as the gold standard of encryption algorithms".
This algorithm uses 128-bit blocks, a 256-bit key, and 14 rounds of encryption. It's particularly effective for securing databases or large files, offering a strong mix of security and performance.
RSA is a popular asymmetric algorithm based on the complexity of factoring large prime numbers. It typically uses key sizes of 2,048 or 4,096 bits. Research suggests that cracking a 768-bit RSA key would take around 1,500 years of computational effort. QA teams often rely on RSA for secure key exchanges and digital signatures, rather than encrypting large datasets.
Elliptic Curve Cryptography (ECC) is a newer option. A 256-bit ECC key provides the same level of security as a 3,072-bit RSA key, making it ideal for resource-constrained environments like mobile or IoT testing.
Legacy algorithms such as DES, 3DES, and RC4 should be avoided in test environments. These methods are outdated, vulnerable, and don't meet modern compliance standards.
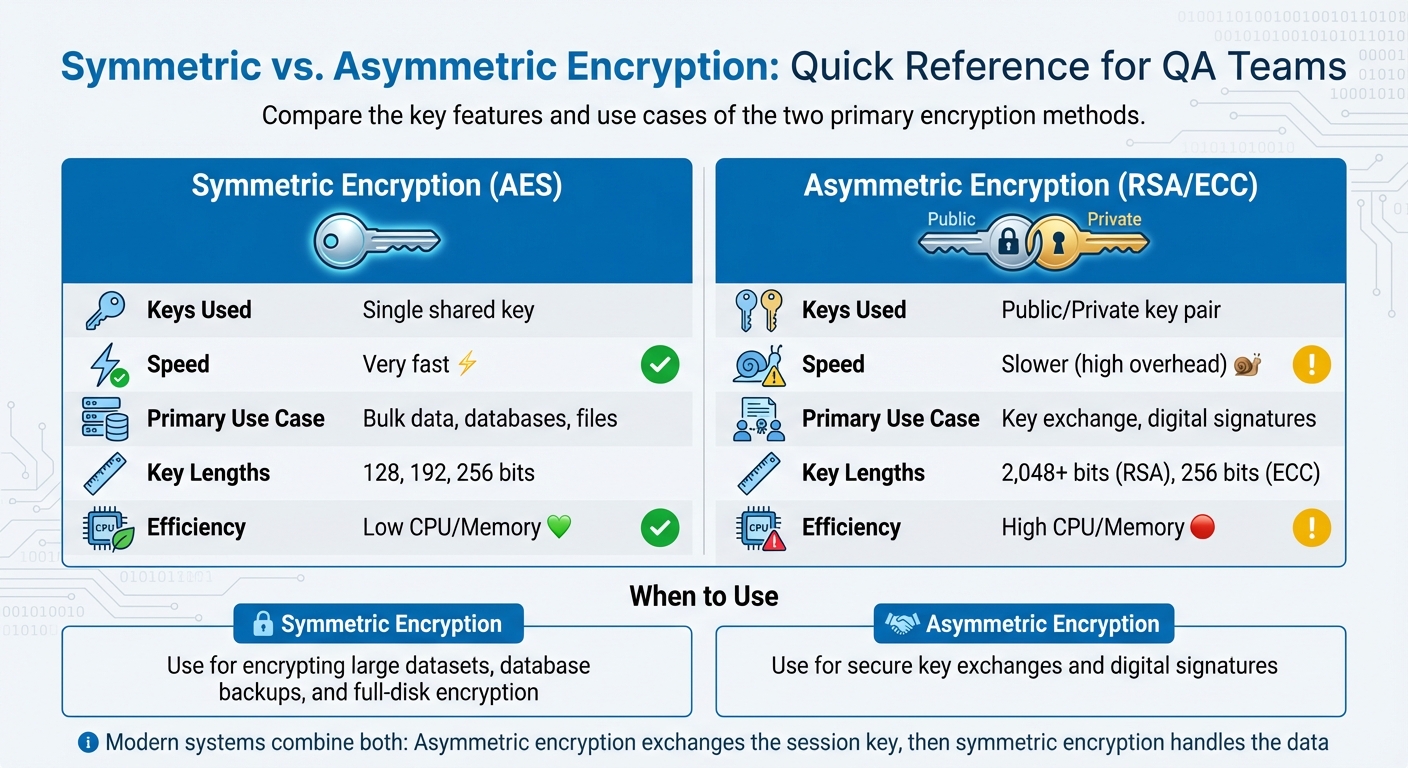
Symmetric vs. Asymmetric Encryption
Symmetric encryption relies on a single key for both encrypting and decrypting data. It’s quick and efficient, making it suitable for handling large amounts of information. As Keyfactor explains:
"In general, symmetric encryption algorithms use less memory and processing power than asymmetric cryptography".
This makes symmetric methods like AES-256 a great choice for securing large datasets, database backups, or full-disk encryption.
On the other hand, asymmetric encryption uses a pair of keys: a public key for encryption and a private key for decryption. While it solves the problem of secure key distribution, it’s slower and more resource-intensive. For instance, RSA decryption can be thousands of times slower than AES encryption.
Modern systems often combine the two approaches. Asymmetric encryption is used to exchange a symmetric "session key", which then handles the faster encryption of data.
| Feature | Symmetric (AES) | Asymmetric (RSA/ECC) |
|---|---|---|
| Keys Used | Single shared key | Public/Private key pair |
| Speed | Very fast | Slower (high overhead) |
| Primary Use Case | Bulk data, databases, files | Key exchange, digital signatures |
| Key Lengths | 128, 192, 256 bits | 2,048+ bits (RSA), 256 bits (ECC) |
| Efficiency | Low CPU/Memory | High CPU/Memory |
Data States: At Rest vs. In Transit
QA teams must ensure encryption works effectively in two key scenarios.
Data at rest refers to stored information in databases, cloud environments, hard drives, and backups. Threats include unauthorized access due to theft, lost devices, or server breaches. Applying AES-256 at multiple levels - application, database, and file system - provides robust protection.
Data in transit involves information traveling across networks, such as API calls, CI/CD pipeline transfers, or inter-service communications. This data is vulnerable to interception and man-in-the-middle attacks. To secure it, use protocols like HTTPS and TLS while disabling outdated ones like SSL 3.0. Typically, asymmetric encryption (RSA or ECC) handles the initial key exchange, with AES securing the ongoing data stream.
QA teams should also test key rotation procedures and monitor logs to ensure sensitive data isn’t accidentally exposed. Encryption might seem straightforward, but validating it across different scenarios requires rigorous attention to detail.
Next, we'll dive into effective key management and security practices to uphold these encryption standards.
Key Management and Security Practices
Encryption is only as strong as its weakest link, and in many cases, that link is key management. If a key is compromised, everything it protects becomes vulnerable. This makes secure key management a non-negotiable priority, especially for QA teams handling sensitive test data.
Key Generation and Rotation
Generating strong keys starts with high-quality randomness. Instead of relying on custom solutions, use operating system tools or hardware security modules (HSMs) to ensure sufficient entropy - essentially, the unpredictability needed to resist attacks.
Automatic key rotation is another crucial practice. For example, AWS KMS rotates keys every 365 days. As Nawaz Dhandala from OneUptime explains:
"Stale keys accumulate risk over time; regular rotation limits blast radius."
To make rotation manageable, envelope encryption is highly effective. This approach separates data encryption keys (DEKs) from key encryption keys (KEKs). When you rotate the KEK, you only need to re-wrap the DEKs instead of re-encrypting your entire dataset. For asymmetric keys that require manual rotation, aliases make the process easier. By pointing applications to the current key version via an alias, you can update keys without diving into the code.
Another key practice is environment separation. Production, staging, and development environments should each have their own key hierarchies. This isolation ensures that a breach in one environment doesn’t compromise others. Limit access using the principle of least privilege: services should only access keys for specific tasks, and human operators should focus on auditing and managing keys - not handling unencrypted key material.
Secure Key Storage
Storing keys improperly - like embedding them in application code, configuration files, or unencrypted databases - can lead to severe breaches. Instead, rely on specialized services like AWS KMS or HashiCorp Vault. AWS KMS, for instance, uses FIPS 140-3 Level 3 validated HSMs to ensure keys never leave the secure boundary in plaintext. These tools integrate seamlessly with QA workflows through APIs, allowing test automation to retrieve keys securely without hardcoding them. This is particularly useful when using AI-powered QA testing platforms that simulate real user interactions.
For centralized security, store keys in a dedicated security account. This reduces the risk of accidental deletion and creates clear audit trails. AWS further safeguards keys by enforcing a mandatory waiting period (7 to 30 days) before permanent deletion, giving you time to recover from mistakes.
Proactive monitoring is another layer of defense. Set up CloudWatch alarms to track unusual activity, such as "Access Denied" errors or attempts to use keys marked as "Pending Deletion". These alerts can help you detect and respond to unauthorized access attempts before they escalate.
Testing Key Compromise Scenarios
To ensure resilience, QA teams must test how systems respond to key compromises or unavailability. Start by simulating key unavailability - disable a test key in AWS KMS or use IAM policies to block access. Your application should log these errors and recover without crashing.
Testing key deletion is equally important. Simulate an immediate deletion using imported key material and confirm that your CloudWatch alarms activate as expected. This not only validates your monitoring setup but also prepares your system to handle catastrophic failures where keys are suddenly gone.
A documented recovery plan is essential. Include contact details, re-keying methods, and a comprehensive key inventory. Regularly practice your re-keying procedures to ensure you can distribute new key material and re-encrypt data with minimal downtime. As OWASP advises:
"A compromise-recovery plan is essential for restoring cryptographic security services in the event of a key compromise."
Encryption Techniques for Test Environments
To ensure test environments are both secure and functional, QA teams need encryption methods that not only safeguard data but also allow these environments to mimic production systems. Let’s explore some effective encryption techniques tailored for test data.
Data Masking and Tokenization
Static Data Masking (SDM) is a widely-used method that permanently replaces sensitive information with realistic, fictional data. This approach is especially useful for QA teams, as it creates fully functional datasets without requiring a live connection to production systems. For example, in 2025, Boeing Employee Credit Union (BECU) used Perforce Delphix to mask 680 million rows of data in just 15 hours, enabling over 200 developers to access production-like environments independently. As Kyle Welsh, BECU's CISO, explained:
"Not only does Delphix reduce our risk footprint by masking sensitive data, but we can also give developers realistic, production-like environments."
Format-Preserving Encryption (FPE) offers another solution by encrypting data while keeping its original structure intact. For instance, a 16-digit credit card number remains 16 digits long, ensuring compatibility with legacy systems that rely on specific schemas and validation rules.
Tokenization, on the other hand, replaces sensitive data with non-sensitive "tokens" stored securely in a vault. Unlike masking, tokenization is reversible, making it ideal for workflows where original values may need to be retrieved.
To maintain consistency across multiple databases, deterministic masking ensures the same input always generates the same masked output. This is crucial for preserving referential integrity in systems where identifiers like Customer IDs or Order Numbers appear in numerous tables. For example, Choice Hotels reduced the time needed to rebuild test systems from two weeks to less than a day using this technique to secure customer data.
Beyond masking, protecting data in transit is equally important, especially in CI/CD pipelines.
End-to-End Encryption in CI/CD Pipelines
Data moving through CI/CD pipelines must be encrypted to avoid exposure. Using TLS 1.3 helps secure data transfers between repositories, build servers, test environments, and deployment targets. Sensitive credentials such as API keys or database passwords should be stored in encrypted vaults like HashiCorp Vault or AWS Secrets Manager, never hardcoded into scripts.
To further enhance security, encrypt build artifacts before storage and enforce role-based access controls (RBAC) to ensure only authorized users can access sensitive data. Automated key and certificate rotation every 90 days reduces the risk of compromise. Additionally, on-the-fly masking, which combines dynamic and static methods, ensures that only de-identified data reaches test environments, protecting sensitive information during transit.
Technique Comparison Table
| Technique | Best For | Reversibility | Format Preservation | QA Suitability |
|---|---|---|---|---|
| Static Data Masking | QA, Development, UAT | Irreversible | High (realistic fake data) | High (read/write datasets) |
| Tokenization | PCI compliance, Analytics | Reversible via vault | High (tokens match format) | Moderate (vault dependency) |
| Format-Preserving Encryption | Legacy systems, Primary Keys | Reversible via key | High (maintains structure) | High (schema compatibility) |
| Standard Encryption | Data at rest/in transit | Reversible via key | Low (ciphertext changes format) | Low (breaks validations) |
Choosing the right technique depends on your specific requirements. For non-reversible needs, static masking is ideal for balancing security and usability. If access to original values is occasionally necessary, tokenization or FPE offer flexibility without compromising data protection.
Automating Encryption Validation in QA Workflows
Relying on manual encryption testing just doesn’t cut it anymore. To keep up with fast-paced development cycles, it’s essential to automate encryption validation within CI/CD pipelines. By embedding these checks directly into the pipeline, you ensure that every code change automatically triggers security tests.
Integrating Encryption Tests into CI/CD
The first step is to connect secret management tools like HashiCorp Vault or AWS Secrets Manager to your CI/CD pipeline. These tools inject encryption keys as environment variables, eliminating the need for hardcoded secrets. You can also use OpenSSL to automate the creation of 256-bit AES keys or RSA key pairs tailored for each test environment.
For thorough encryption testing, combine Static Application Security Testing (SAST) with Dynamic Application Security Testing (DAST). SAST identifies insecure data handling in the code before deployment, while DAST evaluates live applications for vulnerabilities like unencrypted transmissions or authentication bypass. To prevent insecure code from progressing through the pipeline, configure it to block builds immediately when critical vulnerabilities are detected - this "fail-fast" methodology ensures issues are addressed early.
Here’s a real-world example: In March 2025, a logistics platform with a 200-engineer team adopted commit-based test generation. Before this, their QA team spent 40 hours weekly manually setting up regression tests for code changes. After integrating automation, this time dropped to just 6 hours per week - a 34-hour reduction. This freed the team to focus on exploratory testing instead. As Ali El-Shayeb, CEO of Islands, puts it:
"The deployment pipeline isn't continuous when testing requires human configuration between code change and test execution."
Once encryption tests are fully integrated, it’s important to evaluate how they impact pipeline performance.
Performance Considerations
Encryption, while critical, adds computational overhead that can slow applications. Use tools like Apache JMeter in non-GUI mode (-n) to measure how encryption affects response times under load. Configure HTTPS request samplers to test encrypted API endpoints, and use the PerfMon plugin to monitor CPU and memory usage during encryption-intensive operations. Testing with different levels of concurrent users helps pinpoint system breaking points, while comparing encrypted and non-encrypted requests reveals the exact performance impact.
For large files and build artifacts, symmetric encryption (like AES-256) is a better choice than asymmetric encryption (like RSA), as it’s significantly faster.
Rock Smith's Secure Testing Solutions

Rock Smith provides AI-driven testing that works seamlessly with encrypted datasets while maintaining strict security. Its local browser execution ensures sensitive test data stays within your infrastructure - tests run directly on your machines instead of external servers. This makes it especially suitable for handling production-like encrypted data while staying compliant.
The platform also offers real-time monitoring, allowing you to catch encryption failures instantly rather than digging through logs later. Its visual intelligence relies on accessibility attributes instead of fragile DOM selectors, making tests resilient to UI changes. When paired with semantic targeting, this reduces test maintenance by 60% to 85%, freeing QA teams to focus on verifying encryption logic instead of constantly fixing broken tests.
Best Practices for Encryption Implementation and Compliance
To maintain compliance and ensure robust security in test environments, it's essential to build on encryption and key management principles by following these best practices.
Core Implementation Practices
For securing data, use AES-256 for data at rest and TLS 1.2 or higher for data in transit. Stay away from outdated algorithms like DES, MD5, RC4, and SHA-1, as they are vulnerable to modern attacks. Regularly update encryption libraries to apply the latest security patches. To optimize performance, focus encryption efforts on protecting the most sensitive data fields.
Access control is another cornerstone of strong security. Implement Role-Based Access Control (RBAC) combined with Multi-Factor Authentication (MFA). This approach has been shown to reduce unauthorized access incidents by 60%. Following the principle of least privilege, grant access strictly on a need-to-know basis, limiting exposure to sensitive data.
For key management, store encryption keys in Hardware Security Modules (HSMs) or cloud-based Key Management Services (KMS). Always keep keys separate from the data they protect. Rotate keys regularly - testing reveals that a 90-day rotation schedule significantly reduces the risk of key compromise. Use tools like Fortify or SonarQube to identify hardcoded keys before deployment. Organizations that automated 90-day key rotation saw a 60% drop in breach risks tied to compromised keys.
Regular Auditing and Compliance
Quarterly compliance audits are critical for identifying vulnerabilities early. Companies conducting these audits reported a 45% lower rate of successful breaches compared to those auditing annually. These audits should ensure encryption practices meet standards like GDPR Article 32, HIPAA ePHI requirements, and PCI-DSS.
Use centralized logging tools such as Splunk or ELK Stack to monitor access to sensitive data, retaining logs for 6–12 months. Access permissions should also be reviewed quarterly to remove outdated rights, as 56% of breaches are linked to poor internal access management. Additionally, test backup decryption periodically to confirm that encryption keys remain intact and usable.
Don't overlook third-party tools used in testing. Vulnerabilities introduced through external software have affected 40% of organizations. The Spanish Data Protection Authority strongly advises against using real personal data for testing purposes:
"The use of real personal data in test operations is fundamentally unacceptable, as this represents a violation of purpose".
Instead, replace real data with AI-generated synthetic data to sidestep GDPR and HIPAA restrictions while retaining the usefulness of test data.
Post-Quantum Encryption Readiness
Quantum computing may eventually threaten current encryption methods, particularly RSA and ECC. While such quantum computers aren't yet available, it's wise to prepare for long-term data confidentiality needs. NIST is working on quantum-resistant algorithms, and QA teams should stay informed about these developments.
For now, prioritize AES-256 over AES-128, as symmetric encryption is more resilient to quantum-based attacks. Identify datasets that must remain secure for more than a decade, as these will need to transition to post-quantum algorithms first.
Conclusion
By focusing on encryption basics, solid key management, and advanced testing techniques, QA teams can create strong barriers against data breaches. Encrypting test data is a critical step to protect sensitive information in non-production environments. When paired with proper key management, regular audits, and automated workflows, encryption can help prevent up to 95% of data breaches.
A layered approach works best: use AES-256 encryption for both data at rest and in transit, rotate encryption keys every 90 days, and make encryption validation part of your CI/CD pipeline. However, encryption alone isn’t enough. Pair it with tools like data masking, tokenization, and role-based access controls to limit exposure in testing environments. Regular monitoring and audits ensure your test environments meet production-level security standards.
Managing test data effectively is more than just a technical necessity - it’s a way to protect customer trust, enable scalable testing, and shorten time-to-market. Treating test data as a priority, rather than an afterthought, is key.
AI-powered tools such as Rock Smith can further enhance security by automating secure testing workflows. These tools allow teams to conduct tests with real-time monitoring while maintaining security standards, significantly reducing the risk of human error - responsible for nearly 90% of security incidents.
Finally, conducting quarterly audits of encryption methods and access controls can cut breach rates by 45% compared to annual reviews. Investing in proper encryption practices not only strengthens compliance and security but also boosts the efficiency of automated testing workflows. It’s a win-win for both security and operational success.
FAQs
How do we choose between masking, tokenization, and format-preserving encryption for testing?
Masking works well for permanently transforming sensitive data into a format that ensures privacy while still resembling real data. This makes it particularly useful for long-term testing scenarios. On the other hand, tokenization is the go-to method when re-identification is necessary. It replaces sensitive data with reversible tokens, allowing for secure storage and retrieval. Lastly, format-preserving encryption (FPE) is ideal when the original data format needs to be retained, such as in systems that require specific data structures for validation during testing.
What’s the safest way to manage and rotate keys across dev, staging, and production?
The best way to maintain security is by automating regular key rotations and implementing secure key management practices. A dedicated key management system (KMS) can handle these tasks effectively by automating rotations, enforcing strict access controls, and logging key usage. To further strengthen security, make sure to separate environments - use distinct keys for development, staging, and production. Adhering to compliance standards like PCI DSS or HIPAA adds another layer of protection, reducing risks from potential breaches.
How can we automatically verify encryption in CI/CD without slowing builds too much?
To ensure encryption is properly implemented in CI/CD pipelines without slowing things down, rely on lightweight automated tests. These tests should cover key areas like key management, data encryption at rest and in transit, and secure data transfer using TLS/SSL protocols.
Keep the process efficient by optimizing tests to run either in parallel or as incremental steps. The goal is to quickly validate that data and keys are encrypted correctly, rather than diving into complex cryptographic operations. This approach helps maintain a strong security posture without dragging out build times.